

James Wong
Mazda won't rebadge the Toyota Yaris Hybrid for Australia
57 Minutes Ago
Buying a new car is an exciting process, but most people don't know that almost all new cars on the road today can be stolen in under five minutes. We test the tools out.

Founder


Founder
Think your new car is safe just because you have the key with you? Think again! New cars are becoming the victims of thefts without the thief even needing to break into your home.
What’s the background here? Let me paint you the picture.
Alborz had his house broken into and his Jaguar F-Pace stolen recently. The thieves – young kids – broke in, took all his car keys and fled in his car.
It was later recovered, but the keys weren’t. Alborz posted on social media asking for recommendations for a locksmith and a friend told him to try Tapsy Locksmiths.




Alborz called me right after Chamara from Tapsy visited and said, “You won’t believe this, he literally just made two new keys for my car without having my original keys and he said you can do this with virtually any car”.
Well, that’s a slightly dramatised version of our conversation – it wasn’t like the life insurance ads you see on TV as the transcript above would suggest.
So that gave us an idea: let’s take two brand new cars to Chamara – a Hyundai i30 and a Toyota Kluger – and see how long it takes him to break in to the cars and steal them without the original keys being present.
We almost fell off our chairs (well, we weren’t sitting on chairs, but you get where I’m going with it) when he was able to program a new key for the Hyundai and drive off in the car within 30 seconds of arriving to it.
Before we get into how this works, let’s talk about the disclaimer.
We’re not writing this story because we want to teach people how to steal cars. All of the tools Chamara used for this experiment are legal tools that Chamara legitimately uses for his business.
BUT, these tools, according to Chamara, can be purchased by virtually anybody on the internet. And you can imagine how easy it would be for these tools to fall into the wrong hands.
That’s why we’ve gone to lengths in the video to conceal anything that reveals the website or the tools that Chamara uses.

Background
Let’s start with some background. Getting into a new car today involves either using a physical key with a central locking mechanism or a proximity sensing key that stays in your pocket while you trigger a lock on the car.
Regardless of whether your car uses a proximity sensing key, there is almost always a physical key present within the key fob. This is used in the event your proximity key battery dies and you need to manually gain access to the car, and this physical keyhole is sometimes hidden behind a plastic cap or some other garnish.
The exceptions to this are vehicles like a Tesla, which exclusively uses a RFID enabled card or a phone for access. But regardless of this, a Tesla still has a manual front bonnet release hidden behind the bumper for use if the battery dies. Inside the bonnet is a mechanism to supply power to a 12V battery, which then allows authentication with the car.


The physical key hidden within a key for, or the physical key you use within your ignition (just like the Hyundai i30 we sourced) has a fairly unique cut combination. I say fairly unique because some vehicles have multiple versions of the same key around the globe.
That means somewhere else in the world, somebody has a physical key that matches yours and can be used within your vehicle. These are often region limited, so it’s unlikely another vehicle will be sold in your region with the same key profile.
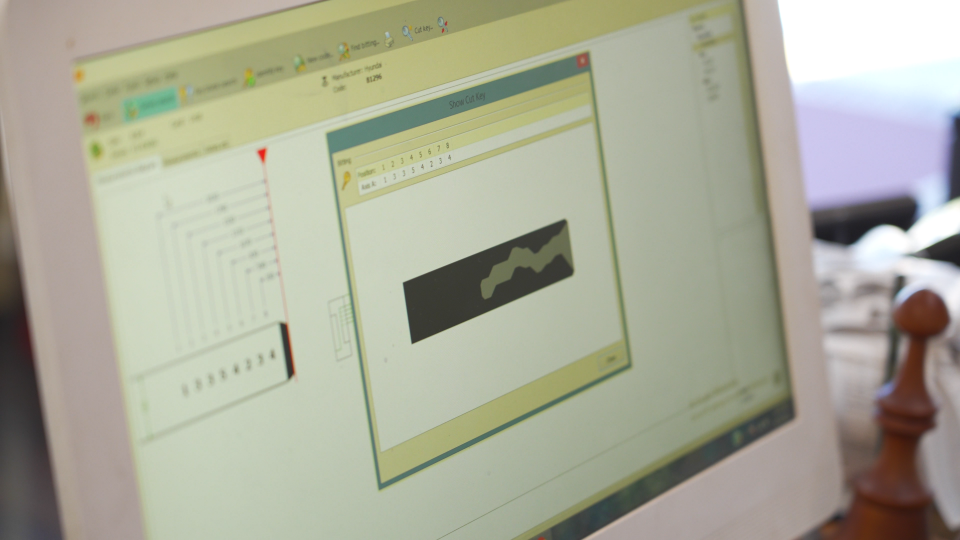
That key profile is assigned what’s called a Key Code. That Key Code can be used by a locksmith using a key cutter with software that decodes the Key Code and tells the key cutting machine how the ridge profiles should be placed on the key.
The Key Code also tells the locksmith what type of key is required – some keys have cuts on one side of the key, while others have cuts on both sides.

In addition to the key code, a locksmith uses a number of other electronic devices that can encode new car keys. Depending on the manufacturer, car brands operate this different to one another. Some allow you to write new keys using just a basic PIN code, while others require new firmware to be written to the car before a key can be encoded for the vehicle.
Either way, doing this outside of the manufacturer typically requires third-party hardware and often this third-party hardware will include some form of decryption that has used the vehicle’s existing algorithm to determine how to access the vehicle’s electronics based on the VIN, which is unique to each vehicle.
The Hyundai
So, you’ve seen the background, but how does this work in practise and why would you go anywhere other than a manufacturer to get a new key for your car? Often manufacturers will charge hundreds, if not thousands of dollars for a genuine key and program service.
A locksmith like Tapsy Locksmiths can do this for a fraction of the price with aftermarket keys or in some cases genuine OEM keys that they program or get the customer to program with the manufacturer.
For Hyundai in particular, it’s alarmingly easy to not only cut a new key that will work in the door, but also program a new key within seconds of gaining access to the car.
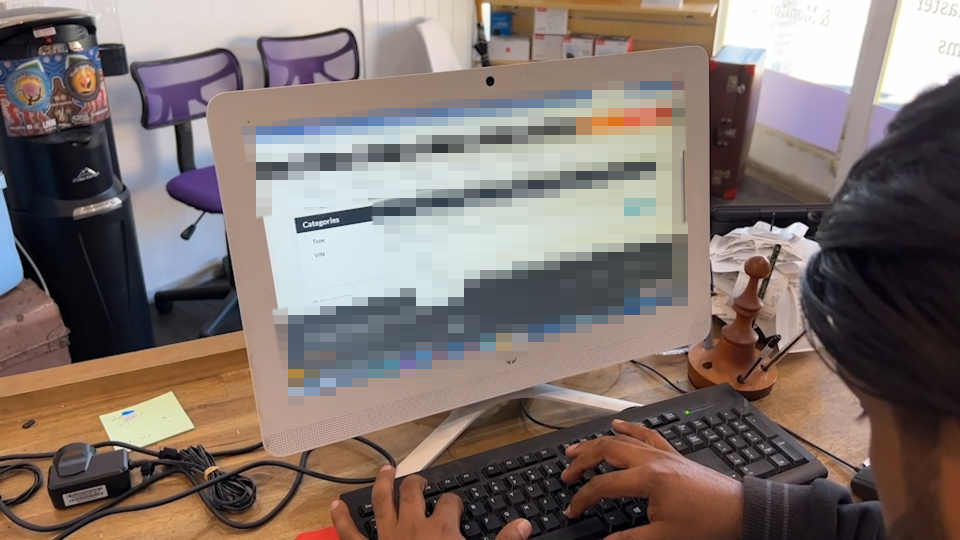
A website that Chamara showed us allows you to enter the vehicle’s VIN. Once that VIN is entered, it spits out the Key Code and the PIN code for the vehicle.
This website is technically meant to only be used by a locksmith, but Chamara tells us when he applied for access there weren’t a great deal of checks and balances in place before access was granted.
We put Chamara to work with our i30. Just using the registration of the vehicle (which a thief could easily obtain just by driving past your vehicle), Chamara pulled the VIN from the Queensland registration office.


He then entered that VIN into the website and it spat out the Key Code and the PIN code for the vehicle. He entered the Key Code into his key cutting machine and cut a new key for the i30. This key is a replica to the key the owner has in their pocket.
We then walked out to the vehicle with the electronic device used to program a new key for the vehicle. Chamara used the key we just cut in the door to open the door – the alarm started going off. He plugged his electronic device into the OBD port and entered the PIN code he obtained from the website, which then disengaged the alarm.
Think about this logically for a second – if you’re sitting at home and hear a car alarm going off on the street, you generally don’t get up to take a look outside unless it has been going off for a few minutes.
Chamara was able to disengage the alarm within 10 seconds of gaining access to the Hyundai. You’re unlikely to even flinch if you hear an alarm blaring and then switching off a short time later.
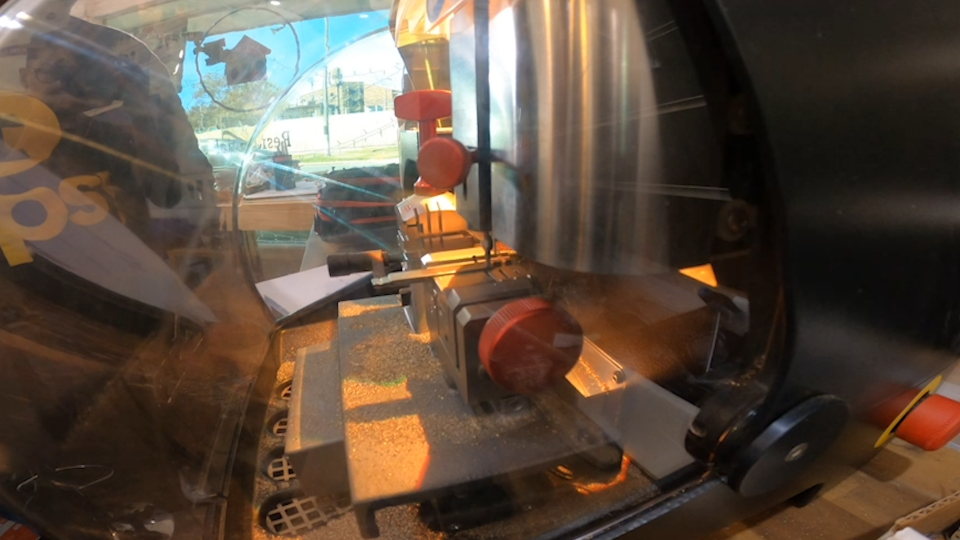
Once he entered the PIN code, Chamara used a blank key to program a new key for the vehicle.
This new key disables the vehicle’s immobiliser and allows Chamara to start the car using the key he had just cut. In less than a minute, he was in a position to drive off in a Hyundai i30 that he didn’t have access to a minute prior.
The Toyota
What about a brand new Toyota? Chamara told us that in the past few years Toyota had updated its security system, and while it used to be as easy as the Hyundai to steal a new Toyota, it recently became harder. But, last year the all-new security system was cracked and another third-party tool was created to override the security system.
The process for the Toyota followed the same path as the Hyundai initially. First you need to cut a key for the car – this is done in the same way as the Hyundai. Using the VIN, obtained via the registration and via the Queensland registration website, Chamara cut a new key for the car.

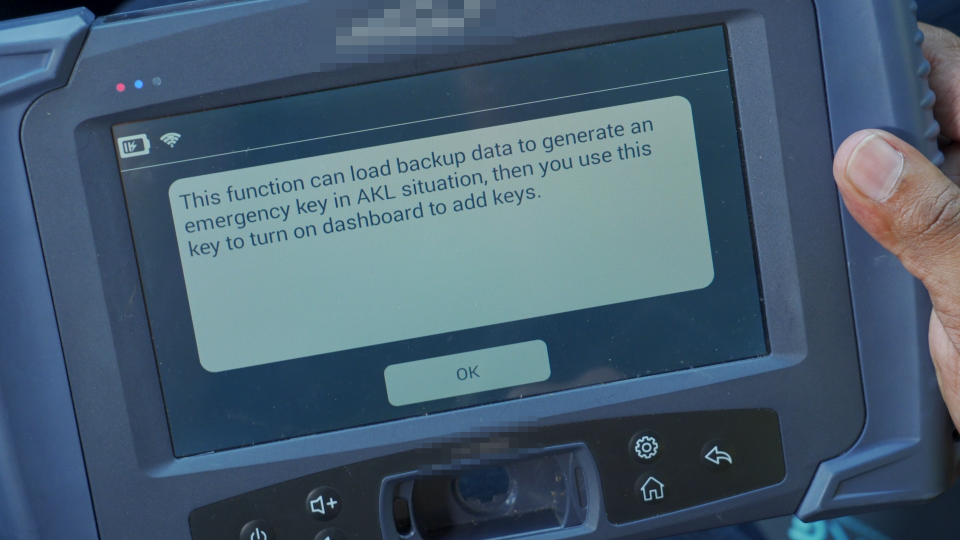
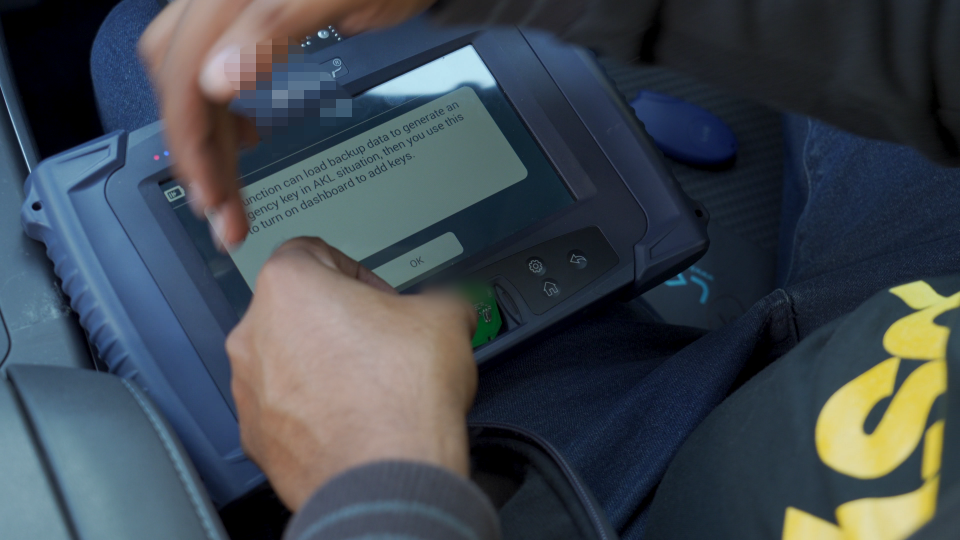
We gained access to the car using the key hole on the door. The alarm started blaring and using another electronic device that plugs into the OBD port, and subsequently uses an interstitial adaptor that plugs into another security module, Chamara was able to write new firmware to the car that would recognise a blank key for as the legitimate key fob for the car.
He was then able to tell the car that all keys had been lost and the blank key fob would tell the car it was okay to write new keys to the car’s key database. Once these new keys were written and programmed on the device, it could be started and driven away.
The whole process took around 2-3 minutes. Same story again – the alarm started blaring as soon as the door was opened, but was quickly disabled after he authenticated with the car.


Other devices thieves use and how you can protect yourself
Another device used by thieves that’s becoming more common is a relay device. One thief will point the relay device at your front door in the hope your proximity key is sitting behind the front door (where people often leave them).
The relay device then relays the signal of the proximity key to the other thief that’s standing at the driver’s door of the vehicle. The car then thinks the key is present and unlocks and allows the thief to start the car.
Obviously if they switch the car off again they won’t be able to start it with the key, but by using one of the devices Chamara has, they could take it to a remote location to program a new set of keys for the car.

You can prevent this type of relay attack by buying a small faraday bag to store your car keys in at home. This prevents the key from emitting a signal beyond the inner lining of the faraday bag.
In the absence of a website to obtain a Key Code, thieves can use a device called a turbo decoder.
This device slots into a key hole and within 15 seconds can recall the inner key profile of the lock. It can then unlock the door as if a key was present.
Again, the thief can then use one of the electronic machines a locksmith has access to, to program a new set of keys and drive off.

How do you prevent a thief being able to access your OBD to actually write new keys? Unfortunately there’s no easy way. You can could disconnect the OBD or perhaps disable access to it entirely. But you’ll need this for any mechanical diagnosis in the future.
The only real way to prevent somebody going away with your car is to go old-school and buy a steering wheel lock. While a thief might be able to program a new key, they wouldn’t be able to then steer the vehicle once it was started.
CarExpert’s Take
We were genuinely shocked at how easy it is to steal a brand new car today, and it’s logical when you think about it. In the case of the Hyundai i30, it would have been undergoing prototype engineering in the years leading up to its release in 2016.
At that point the security system selected for the car would have been a year or two old, let’s call it a 2014 vintage. Fast forward to today and the security system would be almost 10 years old, giving those with malicious intent more than enough time to decide the encryption and figure out a way in.

The only way to prevent this style of thing is with over-the-air security updates that can adjust the security mechanism on the fly. This would again be hard to do if you rely on a key or a proximity device that uses old technology.
Tesla has the right idea by only allowing phone or RFID access to the car. It’s ultimately the best solution that allows the car to roll out security updates as they become known.
Legacy security systems in most other cars on the market are virtually out of date as soon as the car goes on sale.
Either way, it’s an important issue and that needs to be addressed.

Massive shout out to Chamara from Tapsy Locksmiths for helping us out with this story!
Paul Maric is a CarExpert co-founder and YouTube host, combining engineering expertise with two decades in automotive journalism.


James Wong
57 Minutes Ago

Derek Fung
3 Hours Ago


James Wong
10 Hours Ago


Damion Smy
16 Hours Ago


William Stopford
16 Hours Ago


William Stopford
18 Hours Ago
Add CarExpert as a Preferred Source on Google so your search results prioritise writing by actual experts, not AI.